Introduction to Ethics in ESM
In the evolving landscape of Experience Sampling Method (ESM) research, ethical considerations play a pivotal role. ESM studies, known for their real-time data collection and intensive participant involvement, necessitate a heightened focus on ethical standards. For further insights into the foundational aspects of ESM, Introduction to Experience Sampling Method (ESM) provides a comprehensive overview.
Overview of Ethical Considerations in Experience Sampling Method Research
ESM research, by its nature, intersects closely with the personal lives of participants. This intersection raises several ethical issues:
-
- Privacy and Confidentiality: The frequent collection of personal data, sometimes sensitive in nature, requires stringent measures to protect participant privacy.
-
- Informed Consent: Given the intensive nature of ESM studies, obtaining informed consent is crucial. Participants should be fully aware of what participation entails, including the time commitment and the type of data collected.
-
- Data Handling and Security: The handling of ESM data, especially when it includes personal or sensitive information, demands robust security protocols to prevent unauthorized access or data breaches.
For a comprehensive understanding of the latest technological innovations in ESM, resources like Technological Innovations in ESM Data Collection offer in-depth information and insights.
- Data Handling and Security: The handling of ESM data, especially when it includes personal or sensitive information, demands robust security protocols to prevent unauthorized access or data breaches.
Importance of Adhering to Ethical Standards in ESM Studies
Adherence to ethical standards in ESM research is not merely a regulatory requirement; it is a cornerstone of research integrity. Ethical practices in ESM studies ensure:
-
- Participant Trust: Upholding high ethical standards builds trust between researchers and participants, essential for the validity and success of the study.
-
- Research Credibility: Ethical research practices underpin the credibility and reliability of the study’s findings.
-
- Moral Responsibility: Researchers have a moral responsibility to protect the rights and well-being of participants, especially in studies that delve into personal aspects of participants’ lives.
“In the realm of ESM research, ethical considerations are as integral as the method itself. They form the bedrock of trust, integrity, and respect in the pursuit of knowledge.”
As we delve deeper into the specific aspects of ethics in ESM, such as informed consent, privacy concerns, and data security, understanding these foundational principles is crucial. Each component plays a vital role in ensuring that ESM research is conducted responsibly and respectfully.
The Role of Informed Consent in ESM

Informed consent is a fundamental component of ethical research, especially in Experience Sampling Method (ESM) studies, where participants are often asked to share intimate details of their daily lives. This process involves more than just obtaining a signature; it’s about ensuring participants have a clear understanding of what their involvement entails.
Detailed Exploration of Informed Consent in ESM
In ESM research, informed consent must encompass several key elements:
-
- Nature of Participation: Clearly explaining the frequency and type of data collection, such as surveys, physiological measurements, or location tracking.
-
- Purpose of the Study: Articulating the study’s objectives and how the data will contribute to these goals.
-
- Risks and Benefits: Discussing potential risks, discomforts, and benefits to participants, ensuring they understand both the positive and negative aspects of their participation.
-
- Confidentiality and Data Use: Detailing how data will be stored, who will have access to it, and how confidentiality will be maintained.
Strategies for Ensuring Comprehensive and Understandable Consent Processes
-
- Clarity and Simplicity: Use clear, non-technical language to explain study procedures. Avoid jargon to ensure participants from all backgrounds can understand. Include examples or scenarios to illustrate what participation will look like in practice.
-
- Iterative Consent Process: Implement a process where consent is reaffirmed at various stages of the study, especially in long-term projects. Provide opportunities for participants to ask questions and discuss concerns at any point during the study.
-
- Digital Consent Platforms: Utilize digital platforms for consent that can offer interactive elements, such as quizzes or FAQs, to reinforce understanding. Ensure these platforms are accessible and user-friendly, as outlined in Technological Innovations in ESM.
-
- Participant Engagement: Engage with participants throughout the study, as discussed in Participant Engagement in ESM Studies, to maintain their understanding and commitment. Regular check-ins can also serve as a platform for reiterating consent information and addressing any emerging concerns.
“Informed consent in ESM is not just a formality, but a continuous, dynamic process of engagement, ensuring participants are aware, comfortable, and willing throughout the research journey.”
Adhering to these strategies in obtaining informed consent ensures that ESM research is conducted with the utmost respect for participants’ autonomy and understanding. This approach not only fulfills ethical obligations but also enhances the quality and credibility of the research.
Privacy Concerns in ESM

Privacy concerns are particularly pronounced in Experience Sampling Method (ESM) research due to the intensive and personal nature of data collection. Identifying and addressing these concerns is crucial for maintaining participant trust and ethical research standards.
Identifying Privacy Issues Unique to ESM
-
- Intrusiveness of Data Collection: ESM often involves collecting data throughout the day, potentially capturing sensitive moments or private situations. For instance, location tracking or recording mood states can inadvertently reveal information about a participant’s personal life.
-
- Data Sensitivity: The type of data collected in ESM studies, such as emotional states or behavioral patterns, can be highly personal. Studies focusing on specific populations, may gather particularly sensitive information.
-
- Potential for Data Misuse: The richness of ESM data makes it valuable but also vulnerable to misuse if not adequately protected. Ensuring data is used solely for the intended research purposes is a key concern.
Best Practices for Protecting Participant Privacy
-
- Transparent Data Handling Policies: Clearly communicate to participants how their data will be stored, used, and shared. Include privacy policies in the informed consent process as a standard practice.
-
- Robust Data Security Measures: Implement strong encryption and secure data storage solutions to protect participant data. Regularly update security protocols to guard against emerging cyber threats, as highlighted in Technological Innovations in ESM.
-
- Minimization of Identifiable Information: Whenever possible, collect data in an anonymized or de-identified form. Adopt practices like data masking or pseudonymization to further protect participant identity.
-
- Regular Privacy Audits: Conduct periodic reviews and audits of privacy practices to ensure ongoing compliance and address any new privacy concerns.
-
- Participant Control Over Data: Empower participants with control over their data, including options to view, edit, or delete their information. Engage with participants, as recommended in Participant Engagement in ESM Studies, to understand and address their privacy concerns.
“In ESM research, respecting participant privacy is not just an ethical obligation but a cornerstone of building trust and ensuring the integrity of the research process.”
By implementing these best practices, researchers can effectively address privacy concerns in ESM studies, ensuring that participant data is collected, stored, and used responsibly and respectfully.
Data Security in ESM Research

Data security is a paramount concern in Experience Sampling Method (ESM) research, where sensitive data is collected frequently and in real-time. Addressing the unique data security challenges in ESM is crucial for protecting participant information and maintaining the integrity of the research.
Overview of Data Security Challenges in ESM
-
- Vulnerability of Sensitive Data: The sensitive nature of ESM data, including location, personal experiences, and biometric data, makes it a target for unauthorized access and cyber threats.
-
- Real-Time Data Collection: The continuous and real-time nature of data collection in ESM poses challenges in ensuring data security at every point of data transmission and storage. The use of mobile devices for data collection, as discussed in Technological Innovations in ESM, adds layers of complexity to data security.
-
- Compliance with Data Protection Regulations: Adhering to a growing body of data protection laws and regulations, like GDPR or HIPAA, is essential for ESM researchers.
Techniques and Technologies to Secure Sensitive ESM Data
-
- Encryption of Data: Implement end-to-end encryption for data in transit and at rest. This means data is encrypted from the point of collection until it is securely stored. Utilize secure, encrypted databases for data storage.
-
- Secure Data Transfer Protocols: Employ secure protocols like HTTPS for transferring data from participants’ devices to the server. Regularly update and patch software to protect against new vulnerabilities.
-
- Access Control and Authentication: Implement strict access controls to ensure only authorized personnel can access sensitive data. Use multi-factor authentication for an additional layer of security.
-
- Regular Security Audits and Compliance Checks: Conduct regular security audits to identify and rectify potential vulnerabilities. Stay updated with compliance requirements and best practices in data security.
-
- Participant Education on Data Security: Educate participants on best practices for data security, such as secure Wi-Fi usage and device security. Foster a culture of security awareness among participants, as emphasized in Participant Engagement in ESM Studies.
“Securing sensitive data in ESM research is not just a technical task; it’s a fundamental responsibility to safeguard the trust participants place in the research process.”
By adopting these techniques and technologies, ESM researchers can effectively address the data security challenges unique to their field, ensuring the safety and confidentiality of participant data.
Managing Sensitive Information in ESM Research

Handling sensitive or personal information in Experience Sampling Method (ESM) studies is a critical aspect that requires careful consideration and a respectful approach. The nature of ESM often involves delving into the personal and sometimes private aspects of participants’ lives, making the management of this information a key ethical responsibility.
Approaches for Handling Sensitive or Personal Information in ESM Studies
-
- Data Anonymization and Pseudonymization: Implement techniques to anonymize or pseudonymize data wherever possible. This means removing or altering identifiers that link data to individual participants. For example, anonymization can protect student identities while allowing for valuable educational insights.
Discover solutions for ESM challenges in longitudinal research in this insightful article.
- Data Anonymization and Pseudonymization: Implement techniques to anonymize or pseudonymize data wherever possible. This means removing or altering identifiers that link data to individual participants. For example, anonymization can protect student identities while allowing for valuable educational insights.
-
- Consent for Sensitive Data: Obtain specific consent for collecting and using sensitive data. Ensure participants are aware of what constitutes sensitive data and how it will be used. As part of informed consent, outlined in The Role of Informed Consent in ESM, clearly communicate the nature and purpose of collecting sensitive information.
-
- Secure Data Storage and Handling: Store sensitive data in encrypted and secure databases. Limit access to this data to authorized personnel only. Follow strict protocols for data handling and sharing, as discussed in Data Security in ESM Research.
Ensuring Confidentiality and Respectful Treatment of Participant Data
-
- Confidentiality Agreements: Implement confidentiality agreements for all research team members, ensuring they understand their obligation to protect participant data. Regular training on confidentiality and data protection can reinforce this commitment.
-
- Respectful Data Use: Use sensitive data only for the intended research purposes. Avoid unnecessary analysis or exploration of data that falls outside the scope of the study. In studies involving vulnerable populations, extra care should be taken to respect participants’ privacy and emotional well-being.
-
- Transparent Reporting: In research findings and publications, report data in a way that respects participant privacy. Avoid sharing identifiable information or details that could lead to participant identification. Adhere to ethical reporting standards, maintaining the balance between transparency in research and participant confidentiality.
“Managing sensitive information in ESM research is a testament to the respect and dignity afforded to participants, reflecting the ethical heart of the research process.”
By employing these approaches, researchers can effectively manage sensitive information in ESM studies, ensuring confidentiality and maintaining the trust and respect of their participants. This careful handling is not only an ethical imperative but also central to the integrity and success of the research.
Legal and Regulatory Compliance in ESM Research

Navigating the legal and regulatory landscape is a critical aspect of conducting Experience Sampling Method (ESM) research. With the increasing focus on data protection and privacy, compliance with local and international laws is essential for ethical and legal research practice.
Understanding the Legal and Regulatory Landscape Surrounding ESM Research
ESM research often involves collecting personal and sometimes sensitive data, which brings it under the purview of various data protection laws. These laws can vary significantly across different regions and jurisdictions.
-
- Data Protection Regulations: Regulations like the General Data Protection Regulation (GDPR) in the European Union and the Health Insurance Portability and Accountability Act (HIPAA) in the United States set stringent guidelines for data handling and privacy. Researchers must be aware of the specific requirements of these laws, such as obtaining explicit consent for data collection and ensuring the right to data erasure.
-
- Cross-Border Data Transfer: ESM studies often involve cross-border data transfer, which can be complex due to differing legal frameworks in different countries. It’s crucial to ensure that such transfers comply with international regulations and agreements, such as the EU-US Privacy Shield framework.
Ensuring Compliance with Local and International Data Protection Laws
-
- Staying Informed: Regularly update knowledge about relevant data protection laws and regulations. This is especially important as laws evolve, like the ongoing developments in Future ESM Trends and Predictions. Consult legal experts when necessary, particularly when conducting cross-border research.
-
- Implementing Compliance Measures: Develop and maintain a comprehensive data protection and privacy policy tailored to the specific requirements of ESM research. Include measures for data security, consent, data subject rights, and data breach protocols, as outlined in Ethical Considerations in ESM Research.
-
- Participant Rights and Transparency: Clearly communicate to participants their rights under data protection laws, including the right to access, rectify, or delete their data. Ensure transparency in how participant data will be used, stored, and protected.
-
- Auditing and Documentation: Conduct regular audits to ensure ongoing compliance with data protection laws. Keep detailed records of data processing activities, consent forms, and data protection policies.
“Legal and regulatory compliance in ESM research is not just about following rules; it’s about fostering a culture of respect, responsibility, and accountability in handling participant data.”
By adhering to these legal and regulatory requirements, ESM researchers can ensure that their studies not only comply with the law but also uphold the highest standards of ethical research.
Ethical Implications of Technology Use in ESM

The integration of advanced technologies in Experience Sampling Method (ESM) research brings with it a range of ethical implications. While these technologies can enhance the quality and efficiency of data collection, they also raise important questions about ethical responsibility.
Examining the Ethical Aspects of Using Various Technologies in ESM
-
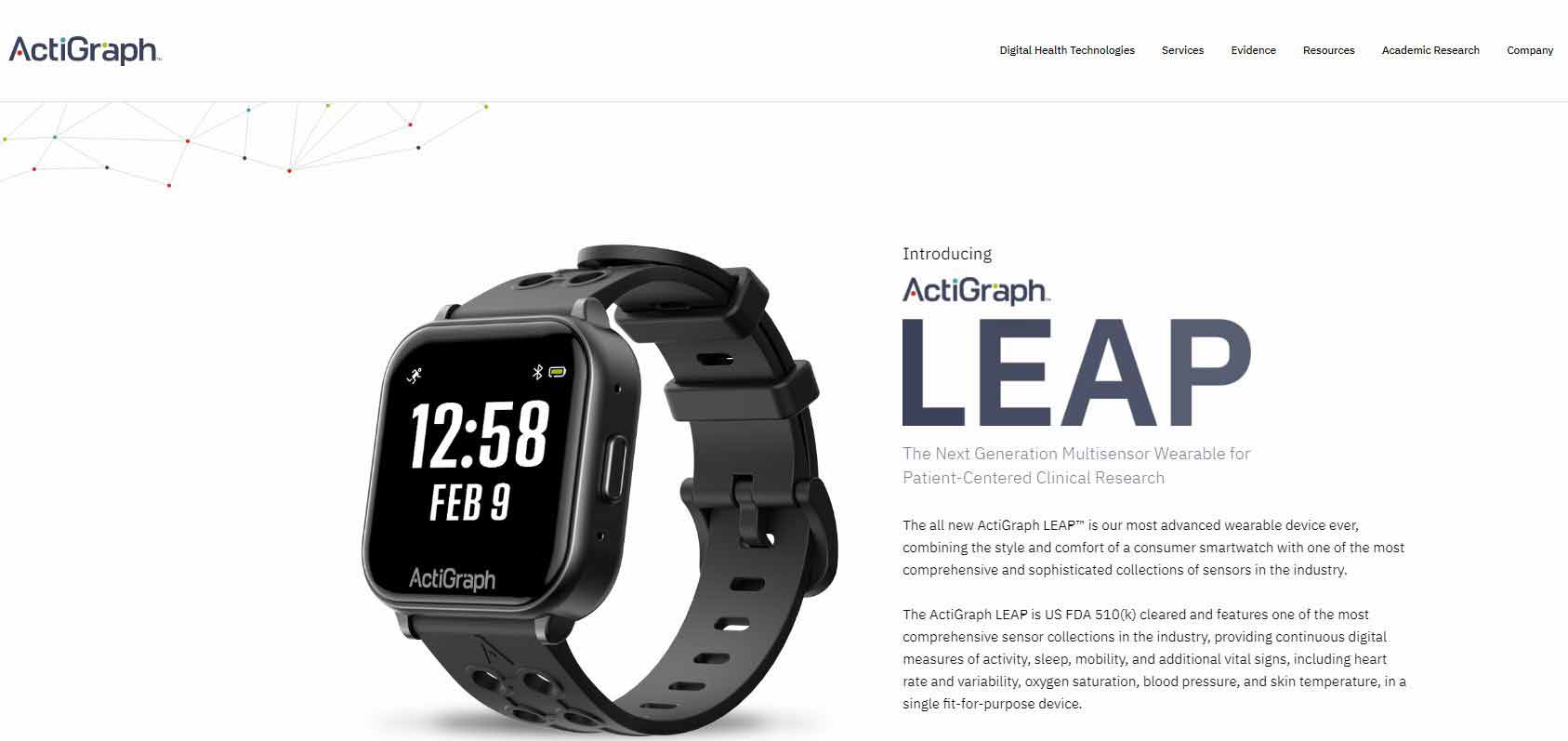
- Invasiveness of Technology: Technologies like GPS tracking or biometric sensors, often used in ESM, can be perceived as invasive. It’s crucial to consider how these technologies might impact participants’ privacy and autonomy.
-
- Consent in the Age of Technology: With complex technologies, ensuring that participants fully understand what they are consenting to can be challenging. Transparent and clear communication, as emphasized in The Role of Informed Consent in ESM, is vital to ensure participants are truly informed.
-
- Data Accuracy and Interpretation: Advanced technologies can collect vast amounts of data, but the interpretation of this data carries ethical implications. Misinterpretation or oversimplification can lead to ethical dilemmas, especially in sensitive areas.
For more insights into the impact of prompt frequency in ESM and strategies to optimize it, Improving Compliance in ESM Data Collection offers valuable information and practical approaches.
- Data Accuracy and Interpretation: Advanced technologies can collect vast amounts of data, but the interpretation of this data carries ethical implications. Misinterpretation or oversimplification can lead to ethical dilemmas, especially in sensitive areas.
Balancing Technological Advancement with Ethical Responsibility
-
- Responsible Use of Technology: Employ technologies in a way that respects participant dignity and privacy. This means being judicious about the type and amount of data collected. Prioritize participant welfare over technological capabilities, ensuring that the use of technology is driven by research needs, not just feasibility.
-
- Ethical Review and Oversight: Regularly review research protocols involving technology use with ethical oversight bodies to ensure they adhere to ethical standards.
-
- Ongoing Dialogue and Reflection: Engage in continual dialogue with peers, participants, and ethicists about the ethical use of technology in ESM. Reflect on the potential long-term impacts of technology use in research, considering evolving societal norms and values.
“In the realm of ESM, technology is a powerful tool, but it comes with the responsibility to use it ethically, respecting the rights and well-being of participants.”
Balancing the benefits of technological advancements with ethical responsibilities is crucial in ESM research. By adopting a thoughtful and conscientious approach, researchers can harness the power of technology while upholding the highest ethical standards.
Conclusion
Upholding Ethical Standards in ESM Research
Ethical considerations in Experience Sampling Method (ESM) research are not merely a compliance checklist; they are the foundation that upholds the integrity and validity of any study. As ESM continues to evolve, integrating more sophisticated technologies and methodologies, the ethical compass guiding this research becomes ever more crucial.
Summarizing the Key Aspects of Ethical Considerations in ESM
-
- Informed Consent: Ensuring comprehensive and understandable consent processes is vital for respecting participant autonomy.
-
- Privacy Concerns: Balancing the in-depth data collection of ESM with robust privacy protections safeguards participant trust.
-
- Data Security: Implementing stringent data security measures protects sensitive information from misuse or breaches.
-
- Managing Sensitive Information: Handling personal and sensitive data with care and respect reflects the ethical commitment of the research.
-
- Legal and Regulatory Compliance: Staying abreast of and compliant with evolving legal standards is essential for ethical ESM practice.
-
- Ethical Use of Technology: Technology in ESM should be used responsibly, prioritizing participant welfare and ethical research objectives.
Emphasizing the Role of Ethics in the Integrity and Success of ESM Research
Ethics in ESM research goes beyond mere rule-following; it’s about cultivating a research environment that values and protects participants. This ethical lens not only ensures the integrity of the research but also contributes to its success by fostering trust, engagement, and credibility.
“Ethical practice in ESM research is the cornerstone of meaningful and impactful scientific inquiry. It reflects a commitment to the highest standards of research integrity and participant respect.”
The adherence to these ethical principles in ESM research paves the way for studies that are not only scientifically robust but also morally sound and socially responsible.
You Might Also Be Interested
Delve into our comprehensive ESM Article Collection for insightful perspectives on Experience Sampling Method (ESM).
See our article Best Tools for Experience Sampling Method in 2024 to discover the top tools in the field.
Learn how the advanced features of Fibion Insight can aid your ESM research.
Planning an ESM study? For a chat with our ESM expert, book a session with Dr. Miriam Cabrita.
Frequently asked questions about this topic
Why are ethical considerations crucial in ESM research?
Ethical considerations are crucial in ESM research to ensure participant trust, uphold research credibility, and fulfill the moral responsibility of protecting participants, especially in studies delving into personal experiences.
What is the role of informed consent in ESM?
In ESM, informed consent ensures participants understand the nature, purpose, risks, and benefits of participation, including data handling and confidentiality, thereby respecting their autonomy and right to make an informed decision.
How can privacy concerns be addressed in ESM studies?
Privacy concerns in ESM can be addressed through transparent data handling policies, robust data security measures, minimizing identifiable information, regular privacy audits, and empowering participants with control over their data.
What are the challenges of ensuring data security in ESM research?
Challenges include securing sensitive data, protecting data during real-time collection and transfer, and complying with various data protection regulations, necessitating strong encryption, secure transfer protocols, and continuous legal compliance.
How should sensitive information be managed in ESM research?
Managing sensitive information involves data anonymization, obtaining specific consent, secure data storage, maintaining confidentiality agreements, and using data respectfully and only for intended research purposes.
What legal and regulatory compliance issues must be considered in ESM research?
ESM researchers must comply with data protection regulations like GDPR or HIPAA, address cross-border data transfer challenges, and ensure transparent communication of participant rights and data protection measures.


 Delve into our comprehensive
Delve into our comprehensive  See our article
See our article  Learn how the advanced features of
Learn how the advanced features of  Planning an ESM study? For a chat with our ESM expert,
Planning an ESM study? For a chat with our ESM expert,